Summary
Realise the promise of safe, usable data across all of your data sources and environments with Privitar Data Privacy Platform’s modern data architecture. The platform uses de-identification techniques in its armory to protect privacy while maintaining data utility.
Protecting data privacy is an essential element of information governance for any data-driven organisation. Organisations must address privacy or face significant issues further down the line. What most are striving for is to find a balance between protecting privacy while still retaining utility in the use of the personal data they process. This requires a fundamental first step that acknowledges that privacy must be a core consideration and must be designed and engineered into data processes.
Privitar was created to help organisations achieve this balance. Privitar Data Privacy Platform has been deployed to protect millions of personal data entries through its advanced Privacy Preserving Technologies to significantly reduce privacy risk.
Problem
Leading organizations need to use personal data to drive innovation. The successful organizations of the future will be those that implement a comprehensive privacy management strategy, enabling data use while managing and mitigating the associated privacy risk.
Those organizations using personal data without appropriate privacy controls risk a range of negative consequences, such as losing customer trust, brand damage, regulatory fines, and litigation. While organizations that lock their data away and fail to use it will fall behind their competitors.
A comprehensive approach to privacy management will ensure that personal data is used safely, building customer trust and acceptance and mitigating regulatory risk. De-identification is a key element of a comprehensive approach to privacy risk management.
De-identification reduces the likelihood that an individual can be identified in a dataset. However, it can also affect data utility and usability. Data utility and usability requirements will often be a key factor driving the choice of controls. In general, de-identification aims to protect privacy while maintaining utility. While mitigating privacy risk can reduce utility, it can allow more value to be extracted from data overall by unlocking data that may be too sensitive to use without privacy risk mitigations in place.
Benefits
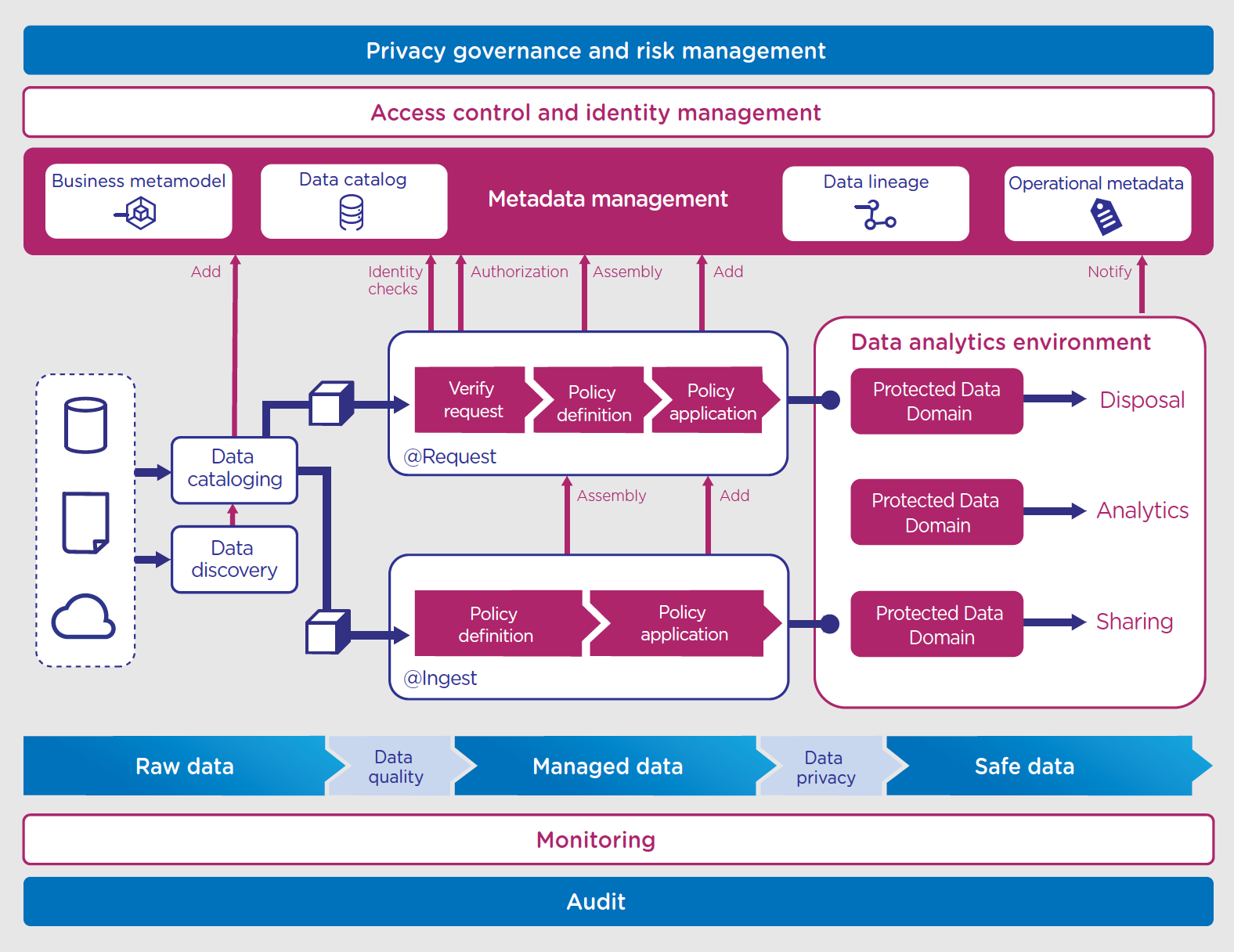
The Privitar Data Privacy Platform provides a modern data architecture that enables organisations to realise the promise of safe, usable data across all of their data sources and environments:
- support the diverse combinations of data, purpose and use
- apply consistent, auditable privacy policies
- streamline and automate data provisioning
- scale to enterprise data volumes
- preserve compatibility with applications and tools
- manage regulatory, reputational, and ultimately financial risk.
Drivers for de-identifying data will vary depending on the use case. Organisations will generally want to use de-identification to:
- Support their broader data strategy, by increasing utilisation for a wider range of data users and use cases and enabling faster data provisioning compared to ad hoc governance processes.
- Build trust among consumers, by positioning data privacy as an element of the organisation’s culture and values.
- Mitigate the privacy risk to the individuals to whom the data relates, or entities other than individuals where confidentiality is important, such as a business.
- Mitigate the risk to the organisation, by enabling compliance with data protection or privacy legislation.
- Complement the organisation’s approach to cyber security, by minimising the risk of personal information being affected by a leak, breach or other form of unauthorised use.
OUTCOMES
BUSINESS USE CASES
Customers: 75M
Challenges & Opportunities
- Crowdsource 3rd-party data analysis, AI/ML while controlling and tracking data distribution and access of de-identified data
- Integrate proprietary and 3rd-party data to enrich data for certain analyses
- Protect data for use in public cloud
Selected Technologies
- AWS
- Cloudera
Phased Implementation
Two phases for access to data:
- internal AI/ML
- 3rd-party crowdsourcing
Three phases of publishing of data:
- customer profile, history
- marketing, enriched customer history
- financial, risk
Business Benefit
Anticipate accelerated and additional insights from expanding number of data scientists building models using the data.
Customers: 40M
Challenges & Opportunities
- Use customer profiles and histories to achieve improved customer experiences, more digital engagement and ultimately increased revenue from existing and new customers
- Comply with the privacy policies that prohibit sensitive personal data from being copied from on-site data centers to the cloud
- Use public cloud infrastructure
Selected Technologies
- AWS
- Hadoop
- Hortonworks
- Tableau
Personalisation and Engagement Dataflow (Use-Cases)
- De-identify customer data on premise
- Transfer de-identified data to the cloud
- Run through analytic models
- Transfer model recommendations back on premise
- Re-identify individuals associated with recommended actions
- Feed into marketing campaign and customer systems
Business Benefit
Project $100M+ over 3 years from optimising pricing, better targeting, enhanced omnichannel customer experience and improved customer service experience at a lower cost
DOWNLOADS & VIDEOS
What is Privacy Engineering? [1 min 36sec]
Jason du Preez, Chief Executive Officer and co-founder of Privitar, explains how to derive critical business insights from sensitive data in a safe and secure way.
What is data privacy engineering and why we need to adopt a privacy by design approach. [1 min 26 sec]
Brief Privitar overview.



